SLA management
SLA management
Your team promised a 15-minute response on critical incidents. But when the CEO's laptop died at 4:47 PM on a Friday, nobody knew who to escalate to, or that the clock was already ticking. This schema fixes that.
SLA Management gives you three focused object types that structure how your organisation defines response targets, wires up escalation rules, and links everything back to the services you actually run. When paired with the Priority Matrix, you get end-to-end incident management: priority calculation feeds SLA selection, SLA targets trigger escalation rules.
What you get
| Object Type | Purpose | Key Attributes |
|---|---|---|
| SLA Policy | Response and resolution targets per priority level | Name, Priority, Response Target, Resolution Target, Support Hours, Calendar Type, Breach Notification |
| Escalation Rule | What happens when targets are at risk or breached | Name, Trigger, Escalation Target, Notification Method, Auto-Reassign, Escalation Level |
| Service Offering | Services linked to their governing SLA policy | Name, Service Type, SLA Policy (Governed By), Service Owner, Availability Target, Customer Facing |
3 object types · 3 reference types
Pro tip: Start with four SLA policies (one per priority level: Critical, High, Medium, Low) and four matching escalation rules. You can always add more later, but starting lean means you can actually enforce what you have defined.
When to use this schema
Deploy SLA Management if your organisation needs to:
-
Formalise response and resolution targets per priority level, replacing informal "we try to respond quickly" expectations
-
Set up structured escalation rules that fire before SLA breaches occur, not just after
-
Link services to their governing SLA policies so every service has documented commitments
-
Support managed service provider operations with contractually different SLA tiers per client
This schema works best alongside the Priority Matrix, which provides the priority levels that SLA policies reference. Together they cover the full chain: incident classification through to escalation.
Not quite right? If you only need to classify incidents by impact and urgency without SLA enforcement, deploy the Priority Matrix on its own. If you need a full service catalogue with categories, knowledge articles, and request types, the Service Catalogue includes its own service level definitions.
Schema at a glance
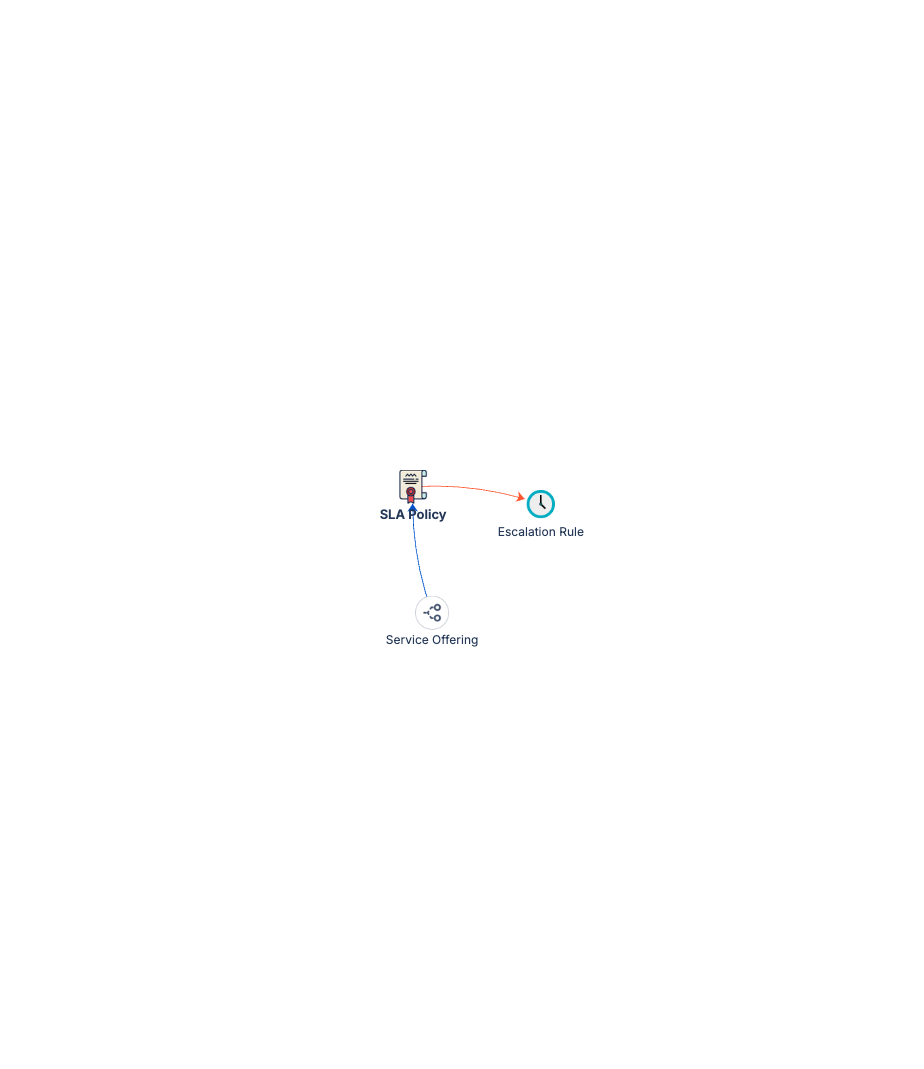
Service Offering ──(Governed By)──▶ SLA Policy ──(Escalates Via)──▶ Escalation Rule
Example:
"Corporate Email" ──Gov──▶ "P2 High: 30m response, 4h resolution" ──Esc──▶ "Pre-Breach: Team Lead via Slack"
Three reference types connect the chain: Governed By (blue) links services to policies, Escalates Via (red) links policies to escalation rules, and Owned By (purple) establishes accountability across all three types.
Documentation
Quick Start Guide Deployment walkthrough covering SLA policy setup, escalation rule configuration, service offering linkage, and starter data for all three object types.
Governance Playbook SLA review cadence, breach analysis practices, escalation tuning, and keeping targets aligned with business needs.
Forms Specification Form layouts for SLA policies, escalation rules, and service offerings.